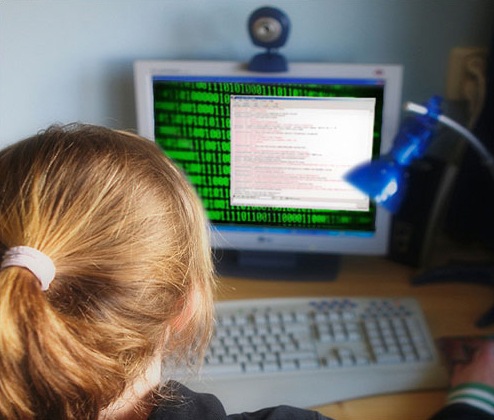
Cyber Alerts for Parents & Kids
Tip #2: Beware of ‘Sextortion’
At the beginning of her summer break in June 2005, a 15-year-old Florida girl logged onto her computer and received a startling instant message. The sender, whom the girl didn’t know, said he had seen her photo online and that he wanted her to send him pictures—of her in the shower. When the girl didn’t comply, the sender showed he knew where she lived and threatened to hurt the girl’s sister if she didn’t agree to his demands.
Worried and hoping to avoid alarming her parents, the girl sent 10 black-and-white images. When her harasser said they weren’t good enough, she sent 10 more, nude and in color. Then he wanted more.
“Once these individuals have pictures, they want more,” said Special Agent Nickolas B. Savage, who interviewed the girl after she and her mother contacted authorities. “They are then able to say, ‘I want you to do x, y, and z. And if you don’t, I’m going to take these photographs and I’m going to send them to people in your school. I’ll send them to your family.’”
Savage, who at the time managed the Innocent Images National Initiative Task Force in the FBI’s Orlando office, spent the better part of the next four years chasing the phantoms that had hacked the 15-year-old’s computer. The winding path eventually led to two assailants—Patrick Connolly and Ivory Dickerson—who jointly terrorized adolescent girls by compromising their computers, demanding sexual photos or videos, and scouring their social networks. The pair also reached out to the girls’ friends—who were duped into downloading malicious software because the e-mails and messages appeared to come from trusted sources.
Connolly and Dickerson, both in prison now, victimized more than 3,800 kids through this “sextortion” technique that preyed on kids’ innocence about the Internet and their fear of being exposed to their friends and family.
Don’t Let It Happen to You
 Here are a few precautions that can keep you from being victimized by “sextortion”:
Here are a few precautions that can keep you from being victimized by “sextortion”:
- Don’t take for granted that your computer’s anti-virus software is a guarantee against intrusions.
- Turn off your computer when you aren’t using it.
- Cover your webcam when not in use.
- Don’t open attachments without independently verifying that they were sent from someone you know.
- It’s okay to be suspicious. If you receive a message with an attachment from your mother at 3 a.m., maybe the message is not really from your mother.
- If your computer has been compromised and you are receiving extortion threats, don’t be afraid to talk to your parents or to call law enforcement.
“Oftentimes children are embarrassed, especially thinking they have somehow contributed to their victimization,” said Savage, who now helps lead the Strategic Outreach and Initiative Section in the Cyber Division. “So fearing they will get in trouble if they report it, they will continue with the victimization and send individuals what they are requesting. What often happens is the victimization never stops.”
In this case, some girls were terrorized over a span of as many as seven years. Some attempted suicide. One dropped out of high school because she was always looking over her shoulder.
To uncover the scheme, the FBI cloned one of the victim’s computers and carried on a two-year undercover correspondence with the hacker, who turned out to be Connolly—a British citizen who was at times in Saudi Arabia and Iraq, where he worked as a military contractor and evidently carried out parts of his extortion scheme. The trail also led to North Carolina, where Dickerson was amassing a huge portfolio of pictures and videos and secretly recording the webcams of compromised computers. Dickerson was found to have about 230 gigabytes of material; Connolly had four times that. Dickerson was sentenced in 2007 to 110 years in prison. Three years later, Connolly was sentenced to 30 years.
Savage says locking up the hackers was one of the most rewarding moments in his career. But he knows there are more victims, some who may not know their tormentors are off the streets.
“The thing was, a lot of these kids are just some folder somewhere,” Savage said, illustrating the cold nature of the crimes and punctuating that once material is posted online, it’s out there for all to see. “No name. Just pictures and videos in a folder. I know that there are so many more victims out there that are wondering, ‘What ever happened to those guys?’ or, ‘Do I still need to be afraid?’”
This story is the second in an occasional series aimed at providing practical web advice and tips for parents and their kids.
Resources:
- Cyber Alerts for Parents & Kids Tip #1: Be Prudent When Posting Images Online
- Innocent Images
- Crimes Against Children



