GameOver Zeus Botnet Disrupted
Collaborative Effort Among International Partners
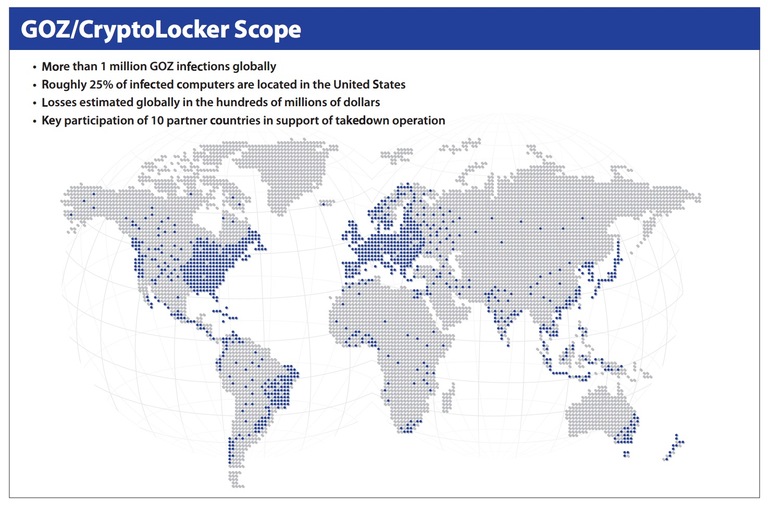
More than a million computers are infected globally, with roughly 25 percent in the U.S.
Update 07/11/14: The Justice Department filed a status report with the United States District Court for the Western District of Pennsylvania, informing the court that the technical and legal measures undertaken to disrupt GameOver Zeus and Cryptolocker have proven successful, and that significant progress has been made in remediating computers infected with GameOver Zeus. Details
On June 2, 2014, the Department of Justice and the FBI announced a multinational effort to disrupt the GameOver Zeus botnet, believed to be responsible for the theft of millions of dollars from businesses and consumers in the U.S. and around the world.
Also announced was the unsealing of criminal charges in Pittsburgh and Omaha against alleged botnet administrator Evgeniy Mikhailovich Bogachev of Anapa, Russian Federation.
GameOver Zeus is an extremely sophisticated type of malware designed specifically to steal banking and other credentials from the computers it infects. It’s predominately spread through spam e-mail or phishing messages.
Unbeknownst to their rightful owners, the infected computers become part of a global network of compromised computers known as a botnet—a powerful online tool that cyber criminals can use for their own nefarious purposes. In the case of GameOver Zeus, its primary purpose is to capture banking credentials from infected computers, then use those credentials to initiate or re-direct wire transfers to accounts overseas that are controlled by the criminals. Losses attributable to GameOver Zeus are estimated to be more than $100 million.
Unlike earlier Zeus variants, GameOver has a decentralized, peer-to-peer command and control infrastructure rather than centralized points of origin, which means that instructions to the infected computers can come from any of the infected computers, making a takedown of the botnet more difficult. But not impossible.
Officials announced that in addition to the criminal charges in the case, the U.S. obtained civil and criminal court orders in federal court in Pittsburgh authorizing measures to sever communications between the infected computers, re-directing these computers away from criminal servers to substitute servers under the government’s control.
The orders authorize the FBI to identity the IP addresses of the victim computers reaching out to the substitute servers and to provide that information to Computer Emergency Readiness Teams (CERTs) around the world, as well as to Internet service providers and other private sector parties who are able to assist victims in removing GameOver Zeus from their computers.
Important note: No contents of victim communications are captured or accessible in the disruption process.
The GameOver Zeus investigation, according to U.S. Deputy Attorney General James Cole, combined “traditional law enforcement techniques and cutting edge technical measures necessary to combat highly sophisticated cyber schemes targeting our citizens and businesses.”
In a related action announced today, U.S. and foreign law enforcement officials seized Cryptolocker command and control servers. Cryptolocker is a type of ransomware that locks victims’ computer files and demands a fee in return for unlocking them. Computers infected with Cryptolocker are often also infected with GameOver Zeus.
Evgeniy Bogachev, added to the FBI’s Cyber’s Most Wanted list, was identified in court documents as the leader of a gang of cyber criminals based in Russia and the Ukraine responsible for the development and operation of both the GameOver Zeus and Cryptolocker schemes.
The actions to take down GameOver Zeus were truly collaborative. “GameOver Zeus is the most sophisticated botnet the FBI and our allies have ever attempted to disrupt,” said FBI Executive Assistant Director Robert Anderson. “The efforts announced today are a direct result of the effective relationships we have with our partners in the private sector, international law enforcement, and within the U.S. government.”
Could Your Computer Be Infected?
- Your computer system operates very slowly.
- Your cursor moves erratically with no input from you.
- You notice unauthorized logins to your bank accounts or unauthorized money transfers.
- Text-based chat windows appear on your computer’s desktop unexpectedly.
- Your computer files lock up and a ransom demand is made to unlock files.
If you notice one or more of these actions on your computer, you may have been infected with the GameOver Zeus malware. The Department of Homeland Security’s Computer Emergency Readiness Team (CERT) has posted additional information on its website about GameOver Zeus, including the specific operating systems impacted, an overview of the malware, and actions you can take to remove the infection from your computer. Visit www.us-cert.gov/ncas/alerts/TA14-150A for details.
Protect Your Computer From Malware
- Make sure you have updated antivirus software on your computer.
- Enable automated patches for your operating system and web browser.
- Have strong passwords, and don’t use the same passwords for everything.
- Use a pop-up blocker.
- Only download software—especially free software—from sites you know and trust (malware can also come in downloadable games, file-sharing programs, and customized toolbars).
- Don’t open attachments in unsolicited e-mails, even if they come from people in your contact list, and never click on a URL contained in an e-mail, even if you think it looks safe. Instead, close out the e-mail and go to the organization’s website directly.
Documents:
- Complaint
- Declaration of Special Agent
- Motion for Temporary Restraining Order
- Memorandum of Law
- Temporary Restraining Order
- Appendix A
- Appendix A Part Two
- Appendix B
- Appendix B Part Two
- Appendix C
- Appendix D
- Appendix E
- Temporary Restraining Order Translated (Нa Руcckom)
- Complaint - Nebraska
- Indictment - Pittsburgh
- Preliminary Injunction
- Amended Preliminary Injunction
- Second Amended Preliminary Injunction
- Fourth Amended Preliminary Injunction
- Appendix A Fourth Amended Preliminary Injunction
- Appendix B Fourth Amended Preliminary Injunction
- Appendix C Fourth Amended Preliminary Injunction
- Appendix D Fourth Amended Preliminary Injunction
- Appendix E Fourth Amended Preliminary Injunction
- Appendix A Part One Permanent Injunction
- Appendix A Part Two Permanent Injunction
- Appendix A Part Three Permanent Injunction
- Appendix A Part Four Permanent Injunction
- Appendix B Part One Permanent Injunction
- Appendix B Part Two Permanent Injunction
- Appendix C Part One Permanent Injunction
- Appendix C Part Two Permanent Injunction
- Appendix E Permanent Injunction
- Order for Permanent Injunction




